Best Prices on Professional Recover Virus Infected Site Guaranteed Results in Banning California 92220
Top
Best Prices on Professional Recover Virus Infected Site Guaranteed Results in Banning California 92220 You found the top source for complete info and resources for Recover Virus Infected Site on the web. Click to vist now.
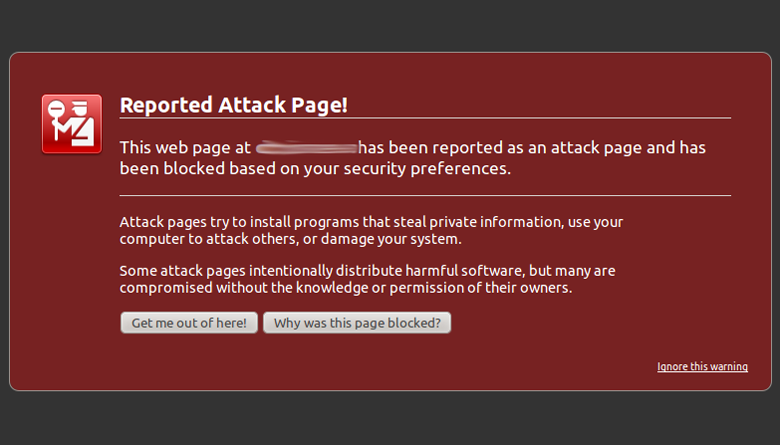
Exploit Scanner Exploit Scanner can scan the files and database of your website and is able to detect if something dubious is present. And if you don't have any malware protection yet, read the reviews, make a choice, and install it now. All identified threats are blocked and you are alerted.
Read More Stop website malware with Site Scanner | 123-reg Whether you're a small business owner, blogger or head of a major corporation, if you're a website owner, you care about the same things: growing... If it is returning the result "Chain issues: Incomplete", a proper intermediate certificate is missing. Side note: It's important you keep regular backups of your database and files.
Below are Some Even more Information on recover virus infected sites
More Resources For recover virus infected sites
Secure communication is an integral part of securing your distributed application to protect sensitive data, including credentials, passed to and from your application, and between application tiers. I wouldn’t blame you if you don’t, typically they are very long winded, so most people haven’t got the time.
Even more Details About recover virus infected sites
Sometimes people are trying to set up a script or add a form or video but it’s simply not working. One way to do that is to block those scripts using mod_rewrite in the .htaccess file. You speak often about your site getting hacked, and how you ran a recorder video and all of that.
A lot more Resources For malware
Designed to identify errors in content related to Section 508 standards and/or the WCAG guidelines. Antivirus that protects you and your personal information from harmful viruses, malware, and spyware. 29,30,32 Increased activity triggers a rise in the number of airborne particles and creates an environment that interferes with aseptic technique and potentially contributes to contamination. Once a system has been compromised, one or more backdoors may be installed in order to allow access in the future,[32] invisibly to the user. To such an extent, database errors should be disabled on a live site, or logged to a file with restricted access instead. Undo Fix My Website @ITsoldUK Nov 20 More RT : 15 Leading Trends for 2018 Thanks.
Last Post Next Post
More from this cat.
Best Prices on Professional Joomla Malware Removal Guaranteed Results in Antelope California 95843
Best Prices on Professional Google Blacklist Removal Sites Guaranteed Results in Altadena California 91001
Best Prices on Professional Joomla Site Hacked Fix Guaranteed Results in Antioch California 94509