Best Prices on Professional Web Sites Malware Cleanup Guaranteed Results in Scotts Valley California 95066
Home
Best Prices on Professional Web Sites Malware Cleanup Guaranteed Results in Scotts Valley California 95066 We are the best source for total info and resources for Web Sites Malware Cleanup on the Internet. Click to vist now.
Here’s how to Kill Antimalware Service Executable in Windows 10 Disable Windows Defender from the Registry Editor RECOMMENDED: Click here to fix common PC issues and speed up your system Type regedit in the search box > hit Enter to launch the Registry Editor. Discover all-new weapons, dog tags and XP boosts throughout the game. When your order is complete and correct, click Submit Order.
OWIN and Katana Katana is a flexible set of components for building and hosting Open Web Interface for . Can you afford to pay a $600 ransom to get your data back? If vulnerabilities exist on the IP address provided, FreeScan will find them and provide detailed information on each risk – including its severity, associated threat, and potential impact. Creates strong encrypted passwords in one click. even for sites you already have logins for. The time frame is also affected by the type of scan (for example, a quick threat search will be completed much quicker than a root scan of the C drive). thorough scans can take multiple hours to complete. 5 million users, and the hackers responsible say that the stolen data includes customer information including real names and addresses, credit card details, and sexual fantasies.
Here are Some More Resources on best malware removal
Below are Some Even more Resources on websites infected malware removal
If Joomla is in subdirectory, then replace it with: define(‘JPATH_CONFIGURATION’,JPATH_ROOT. Do not reboot your computer after running RKill as the malware programs will start again.
More Details About websites infected malware removal
If you want to read more from Craig, subscribe to our weekly tech geek newsletter, Tech Times.A comprehensive WordPress installation, albeit simple to produce, often requires multiple steps -- many of which can easily be omitted accidentally. Download White Paper Ransomware's Path to Extortion Take a deep dive into an attack and discover technologies to secure your business. Automatic Malware And Spyware Protection Home; Useful Information. This can be done by creating an .htaccess file in the directory you wish to protect and then adding a rule inside the file. PCWorld Choose Threat Scan to perform a basic analysis of your computer’s most commonly infected files.
Here are Some Even more Resources on best spyware remover
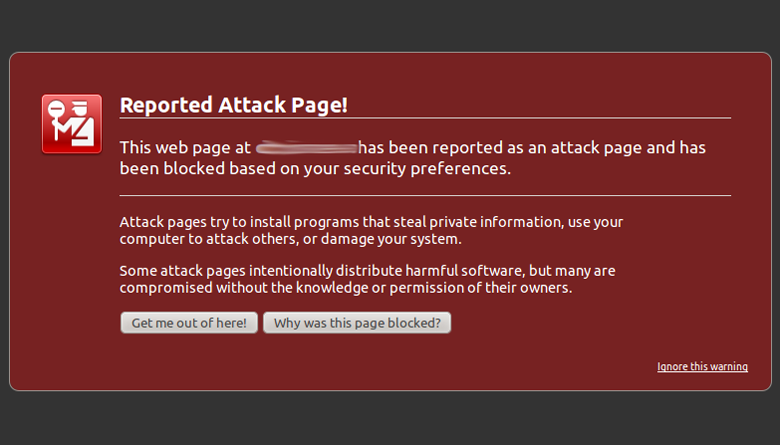
Goodman on CrossTalk: ' Seth Rich' SUBRSRIBE TO TIM BLACK! The attacker can now log in with an administrator account, without having to specify a password. Allowing users to upload scripts: For example, if a component accepts images, you should ensure that only images are allowed to be uploaded. Many forms of malware cause or masquerade as seemingly unrelated Windows and PC issues like Blue Screens of Death, issues with DLL files, crashes, unusual hard drive activity, unfamiliar screens or pop-ups, and other serious Windows problems, so it's important to properly check your computer for malware when working to solve many problems. Sports full award-winning Bitdefender engines Finds Mac malware as well as Windows viruses and other threats etc.
Last Post Next
More from this cat.
Best Prices on Professional Website Security Check Guaranteed Results in Goleta California 93117
Best Prices on Professional Recover Malware Infected Site Guaranteed Results in Kerman California 93630
Best Prices on Professional Site Blacklisted Removal Guaranteed Results in Mckinleyville California 95519